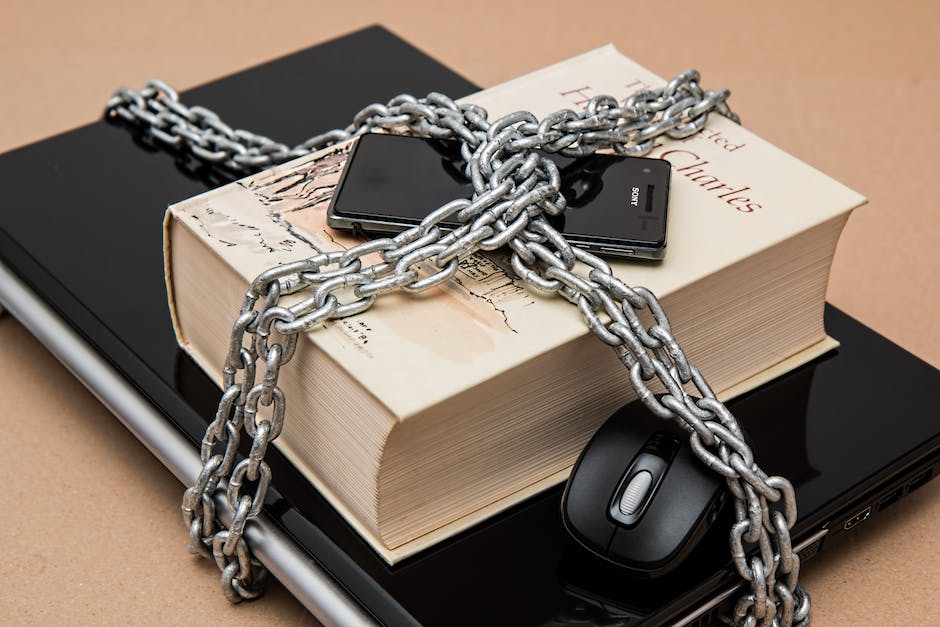
Rapid trends in the development of mobile technologies are closely related to the high risk of information leakage and a low level of mobile device security awareness. In this article, we will look at how to enhance the security of existing mobile applications and lay the foundations for building a secure development process.
What is mobile device security?
Mobile device security refers to the measures taken to protect mobile devices such as smartphones and tablets from unauthorized access, theft, malware, and other security threats. With the increasing reliance on mobile devices for personal and professional use, mobile device security has become a crucial issue for individuals and organizations alike.
Some common security measures for mobile devices include using strong passwords or biometric authentication, keeping software and operating systems up to date, and using mobile security software to detect and prevent malware. It’s also important to be cautious when downloading apps or opening links, as these can often contain security threats.
In today’s digital age, mobile device security is more important than ever. By taking the necessary precautions to protect your mobile device, you can ensure the safety of your personal information and prevent security breaches.
Why is mobile device security important in the current realities?
Only a lazy person today has not set up a touch password on his mobile device and connected a million verifications while continuing to download applications from unofficial sources and install miracle extensions fearlessly. Often such stories end with hacked accounts and the leakage of personal data. Realistically assessing the situation, we all understand that Internet technologies are too mobile to make loud promises to users and guarantee 100% security.
Rapidly increasing competition requires fast solutions, so the speed of application development rises yearly. Everyone wants to be the first to implement new functionality, shortening production cycles, and releases can be released almost daily. However, faster does not mean better. Catalyzing development affects the entire product, including its absolute security. Unfortunately, such applications usually contain beautiful marketing clichés without cryptographic specifics and effective mechanisms for ensuring the confidentiality of information. Many companies have learned from bitter experiences and understand that a security gap can sooner or later become a stain on reputation, which cannot always be eliminated.
Furthermore, more and more users use mobile devices not only as a means of communication but also as an organizer – for scheduling personal and work meetings and storing personal data. Trusting more and more personal information on smartphones and tablets, their owners often forget basic security rules. Meanwhile, the number of crimes related to the theft of personal data is growing every day. Of particular interest to attackers are login data for various financial systems (online banking, electronic wallets), access to websites, mailboxes, online games, email addresses, and phone numbers found on the device.
Types of mobile security
There are various types of mobile security measures that are used to protect mobile devices from potential security threats. Some of the most common types of mobile security include:
- Password protection: This involves setting up a strong password or PIN to lock your device and prevent unauthorized access.
- Biometric authentication: This includes using fingerprints, facial recognition, or iris scans to authenticate the user and unlock the device.
- Encryption: This is a security measure that converts data into a code to prevent unauthorized access. It can be used to encrypt data stored on the device or data transmitted over networks.
- Mobile device management (MDM): This involves using software to manage and secure mobile devices used in an enterprise environment. It can include features such as remote device wiping and the ability to control access to corporate data.
- Mobile application management (MAM): This is a security measure that controls access to and protects mobile apps. It can include features such as app-level encryption and app wrapping.
- Mobile antivirus software: This is a security measure that helps to detect and remove malware from mobile devices.
How to secure mobile devices and applications?
Several aspects should be considered when organizing the protection of your mobile device:
- Physical device protection
It is essential to follow the simple safety rules you try to follow in everyday life so that things do not get stolen. You should always keep your mobile device with you, do not leave it out of sight, and do not pass it on to other people.
- Antivirus software
Use licensed antivirus software for mobile devices because there are also fakes among antiviruses. Free protection tools do not always provide a high level of security.
- Remote device management
Some services allow you to control your device from a distance, such as Apple’s Find My iPhone service (included in a free iCloud subscription and works on iPhone, iPad, iPod touch, and Mac).
- Data storage
Try not to keep contact information in the public domain, and log out of all accounts when you stop working with the device. It is desirable to completely exclude the possibility of saving passwords on a mobile device. If your device is attacked, an attacker can commit a crime without access to passwords and other important information.
- Data encryption
There are special programs that will encrypt your data, that is, protect files on the device and information transmitted over the network from unauthorized users, for example, Kaspersky Endpoint Security for Smartphone, which includes encryption tools.
- Software installation
Installing programs from the developer’s official website will allow you to avoid much higher costs in case of a device replacement or data loss beyond recovery.